SealKeep uses several layers of protection. Here's what each one does and why it matters.
🔑
Your unlock happens on your device
When you unlock, your records are opened in your app memory on your device.
The server stores locked records.
Good password handling and login protections make account guessing attacks harder.
🔒
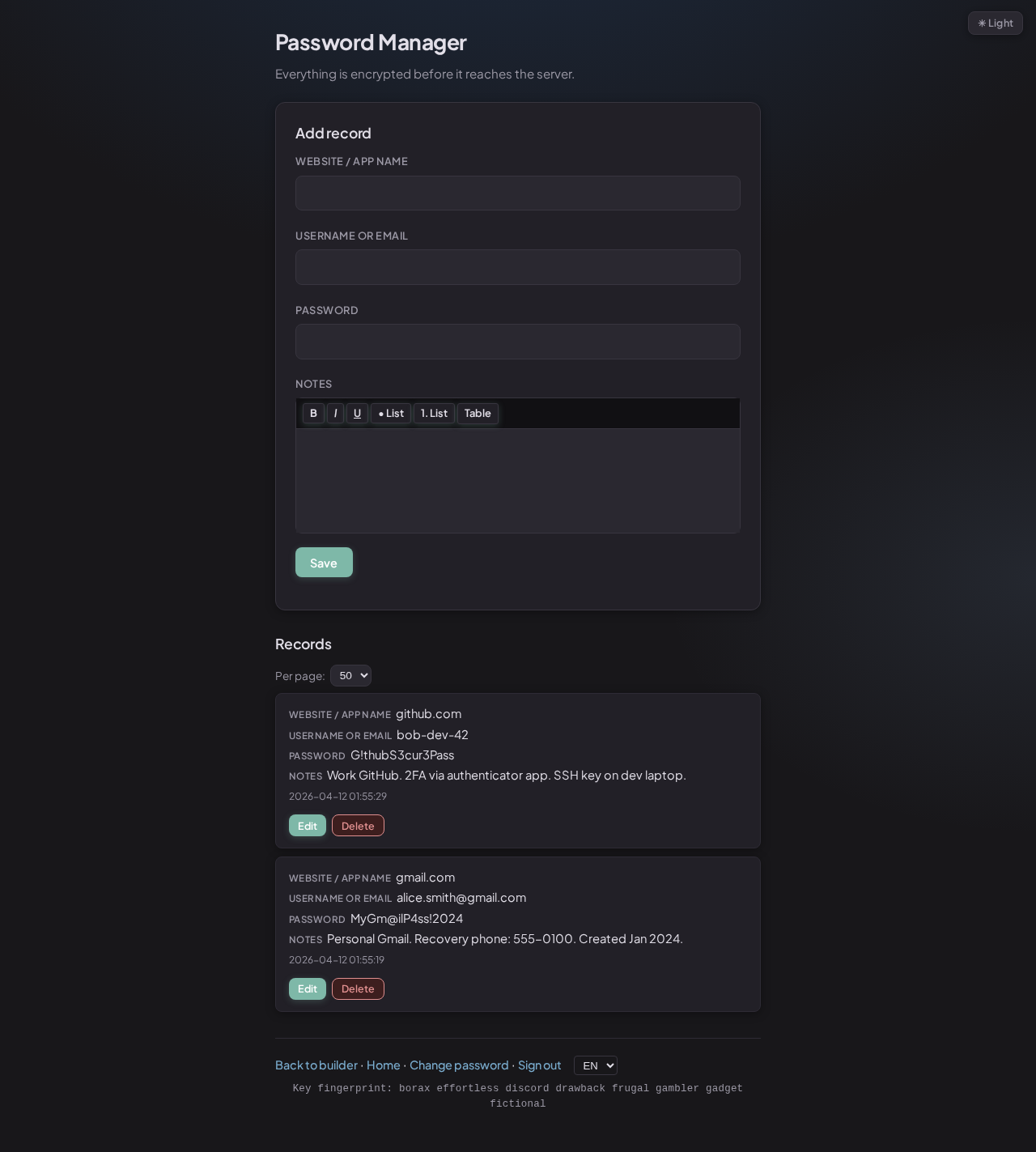
Every record is locked individually
Before a record is sent to the server, your app locks it. Each record is locked
separately so plain content is not stored on the server.
If locked data is changed in transit or storage, record opening can fail instead of
silently showing bad data.
Per-record protection · Locked at rest · Tamper checks
🔁
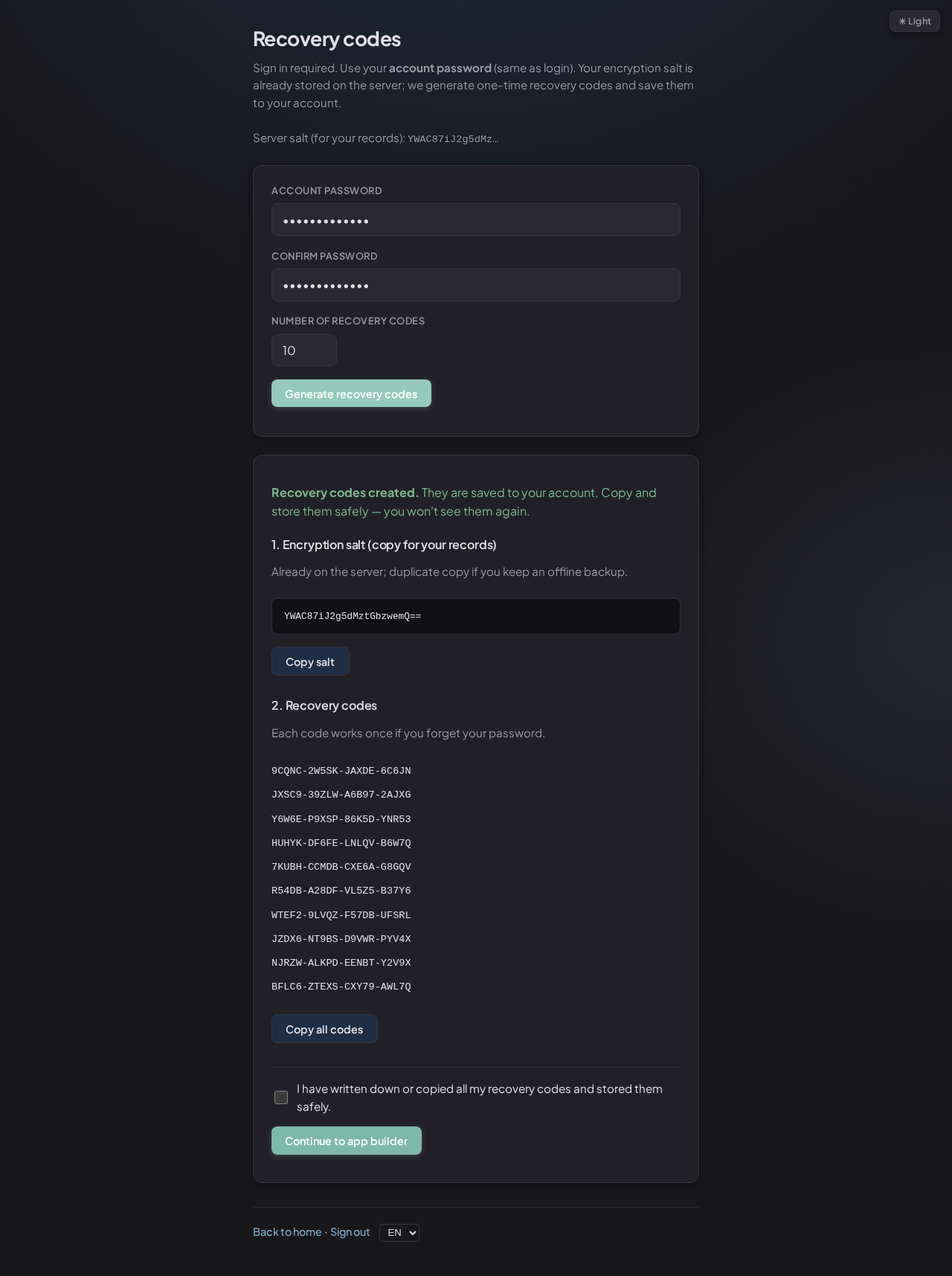
Recovery codes are separate keys
Each recovery code can restore access if you lose your password. Using a code removes
it from the list so it cannot be reused.
Codes are shown once. Save them offline.
One-time codes · Offline safekeeping recommended
🤝
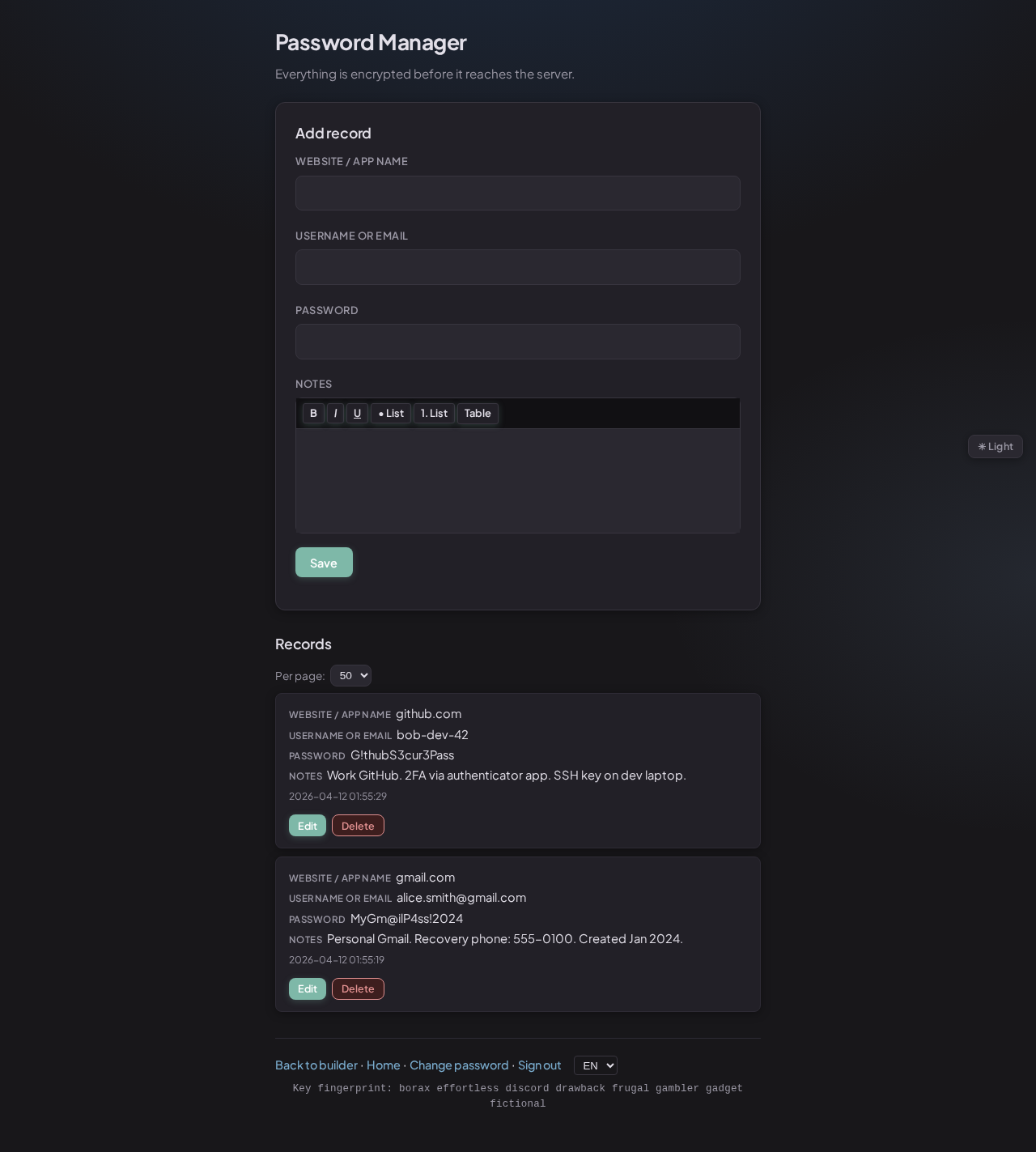
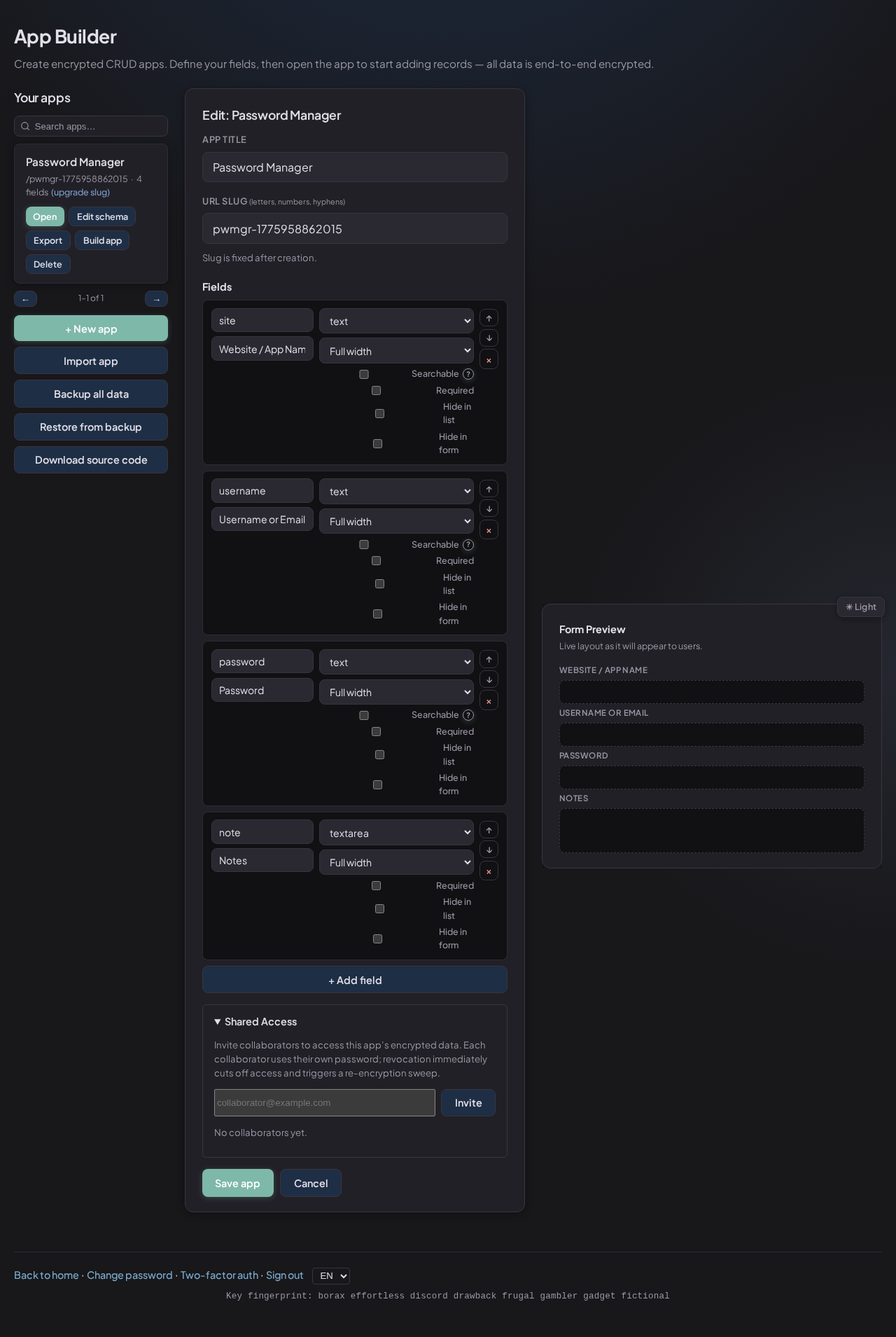
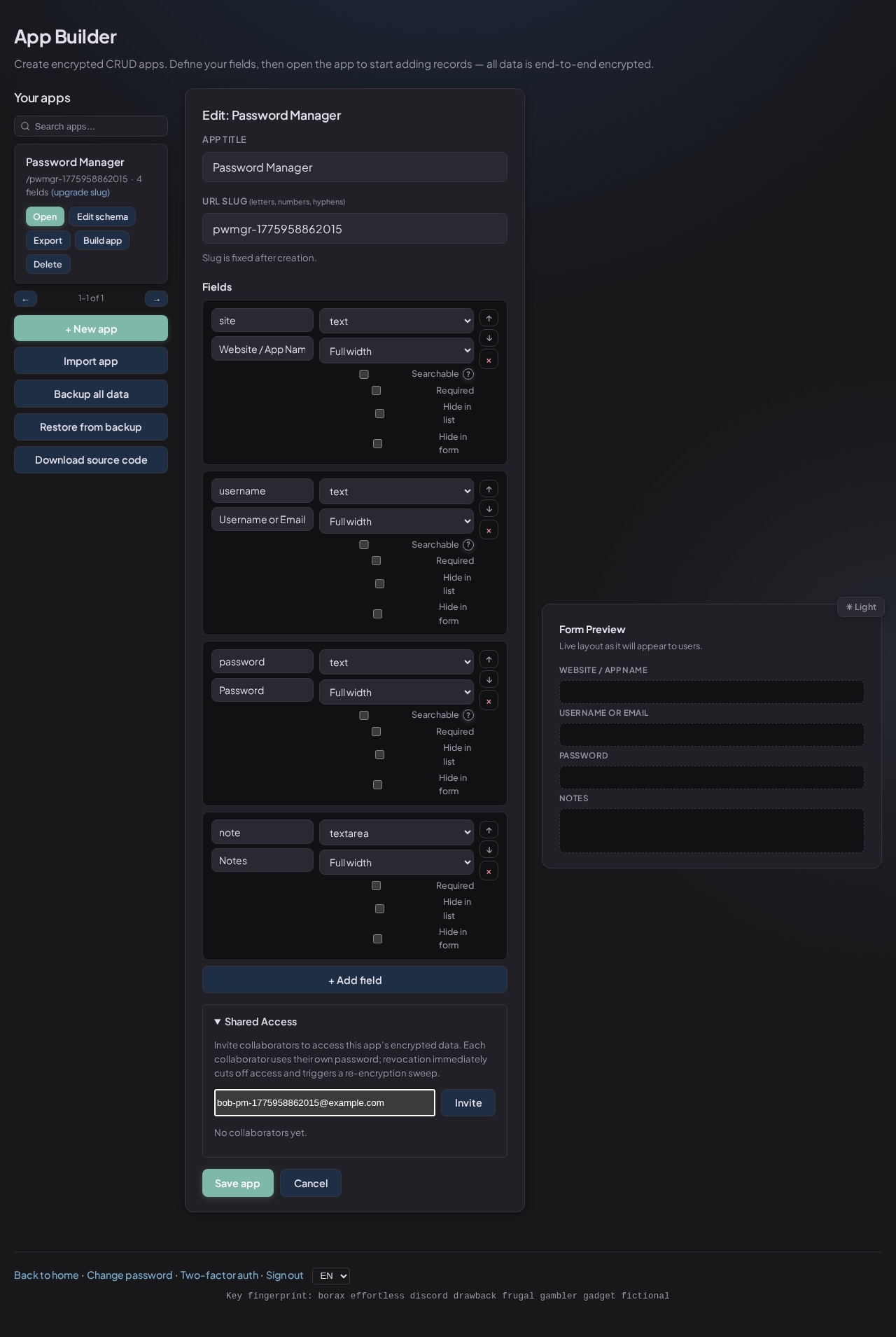
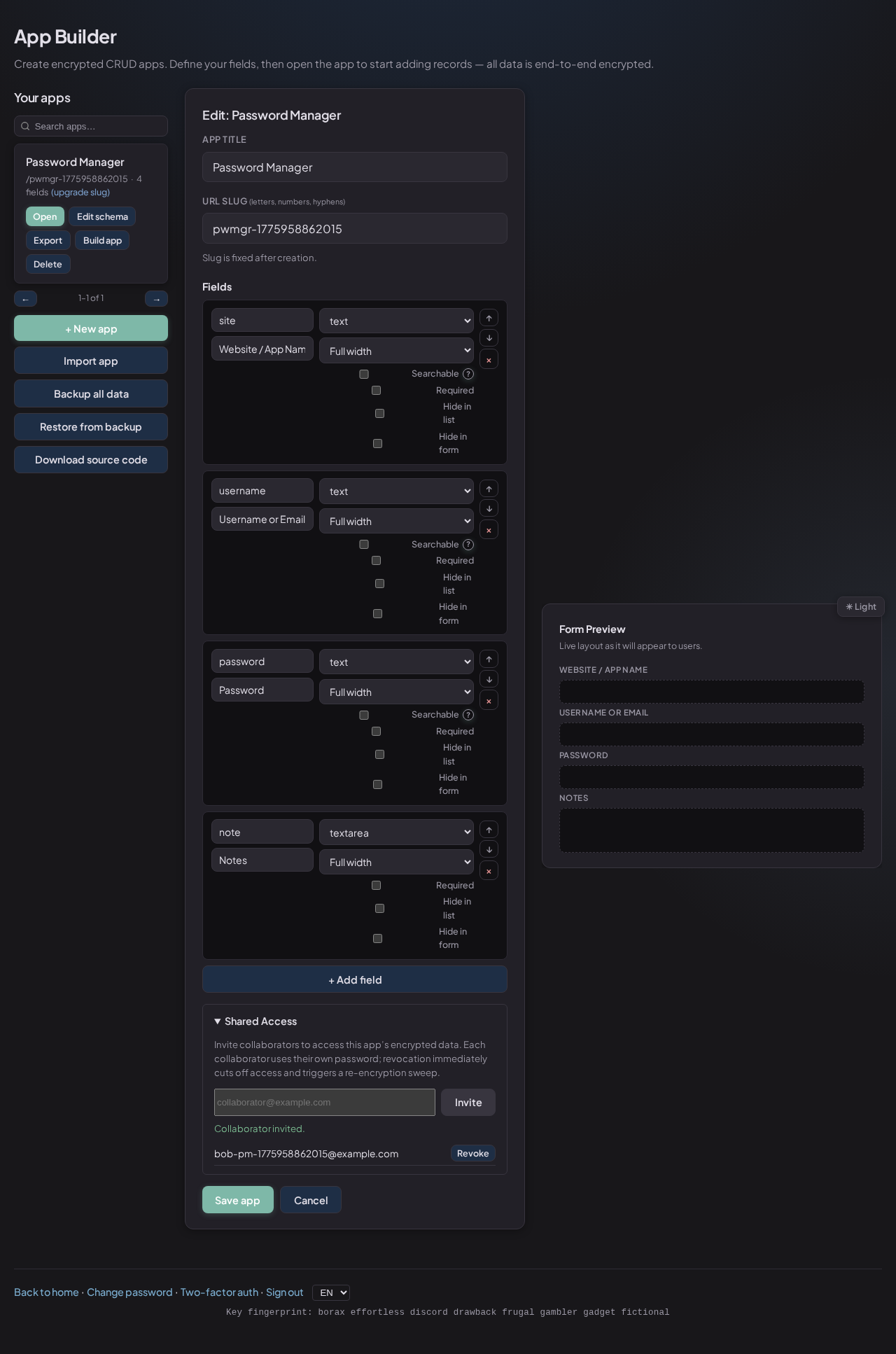
Sharing uses digital envelopes
When you invite a collaborator, SealKeep grants access without sharing your password.
They sign in with their own account.
Revoking access removes their access and refreshes app access state for safety.
Per-user access grants · Revocation support
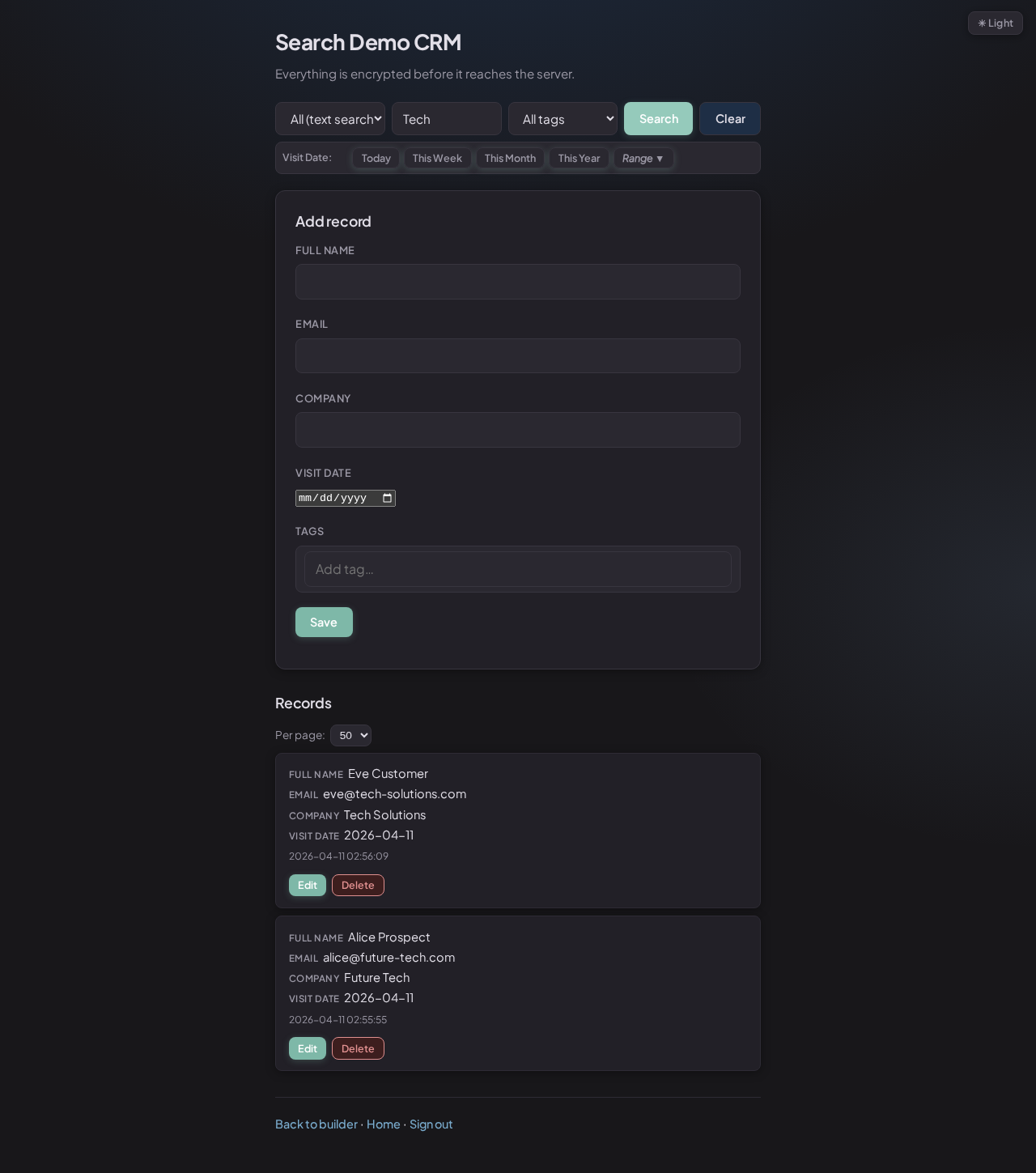
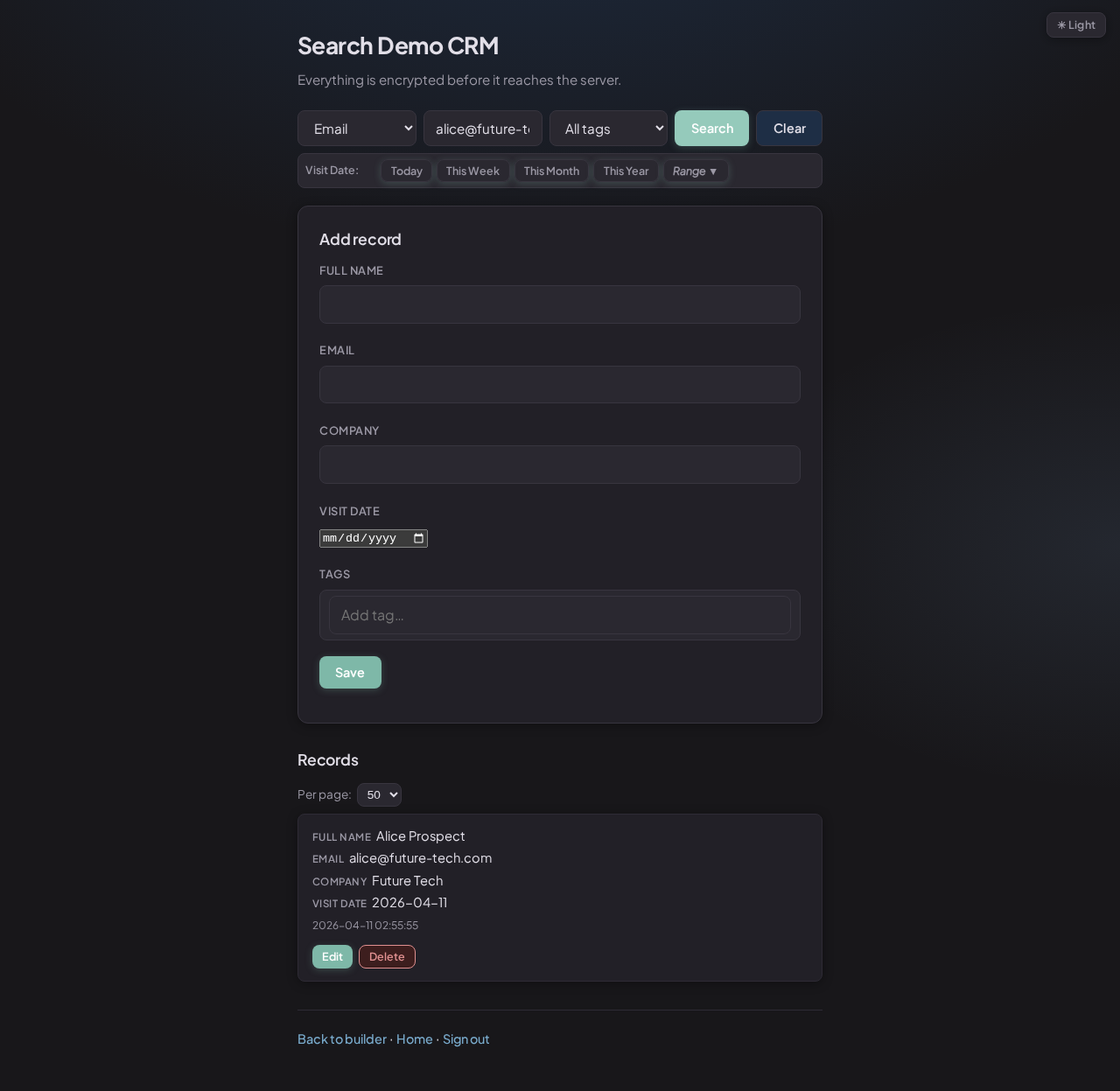
🏷️
Tags are fingerprinted, not stored
Tag labels are represented by private fingerprints on the server so filtering can work
without storing plain tag text.
This lets you filter by tag while keeping labels private in normal use.
Private fingerprints · Locked labels
📱
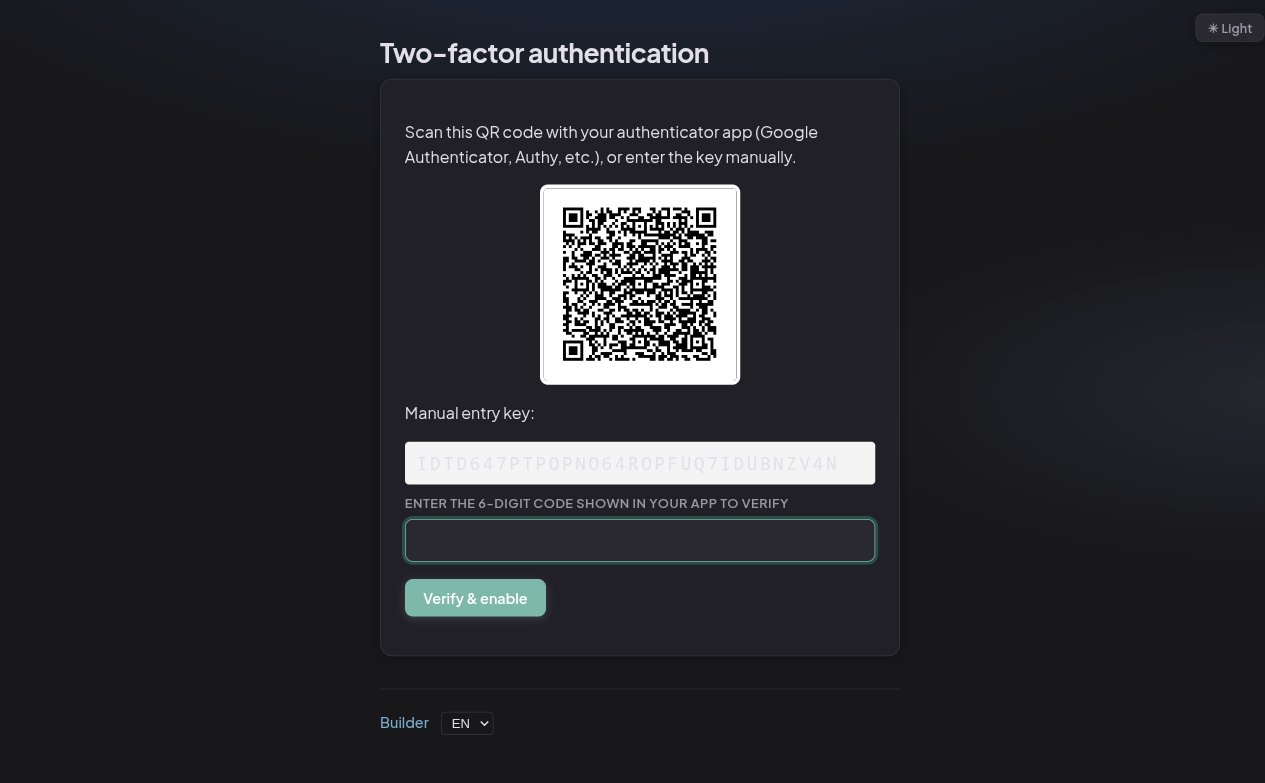
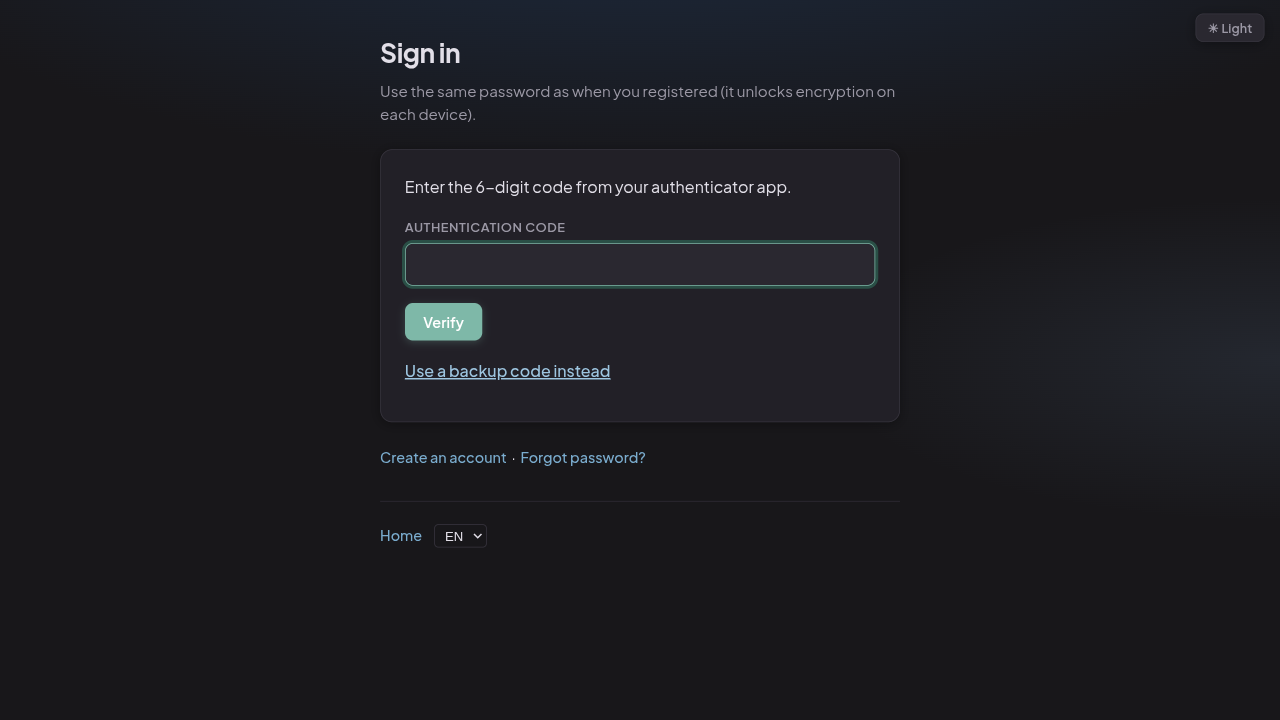
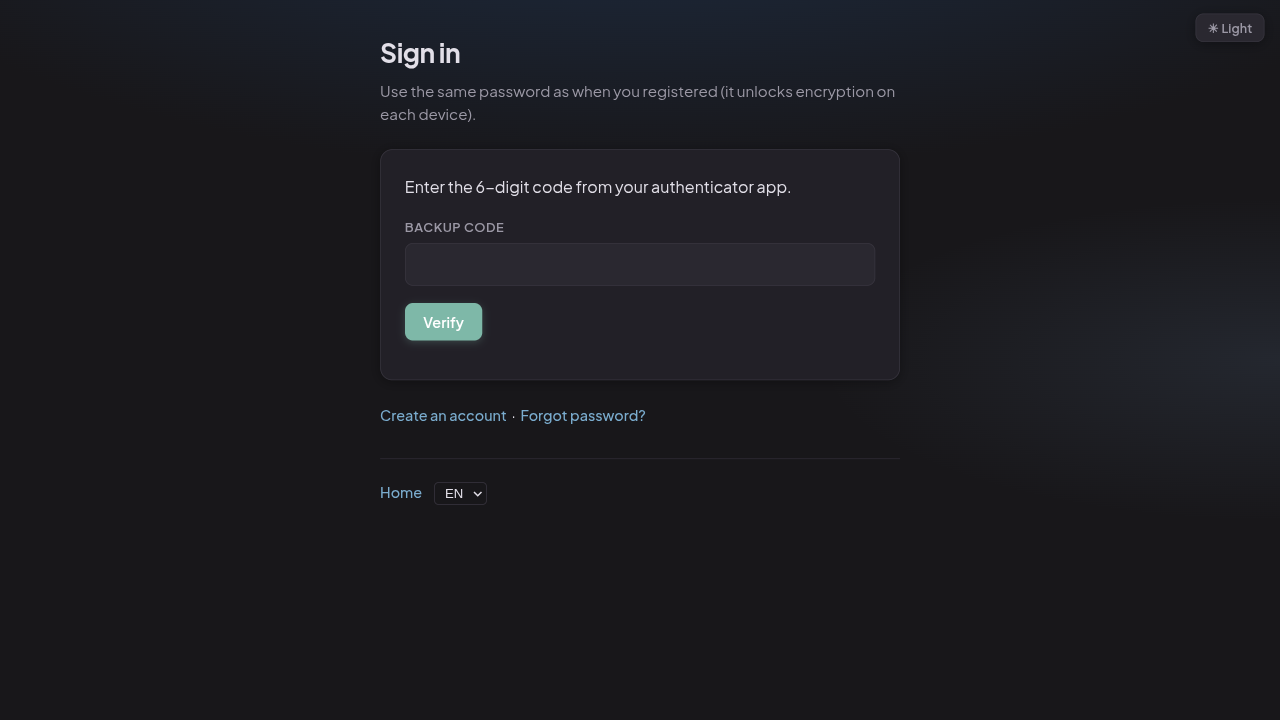
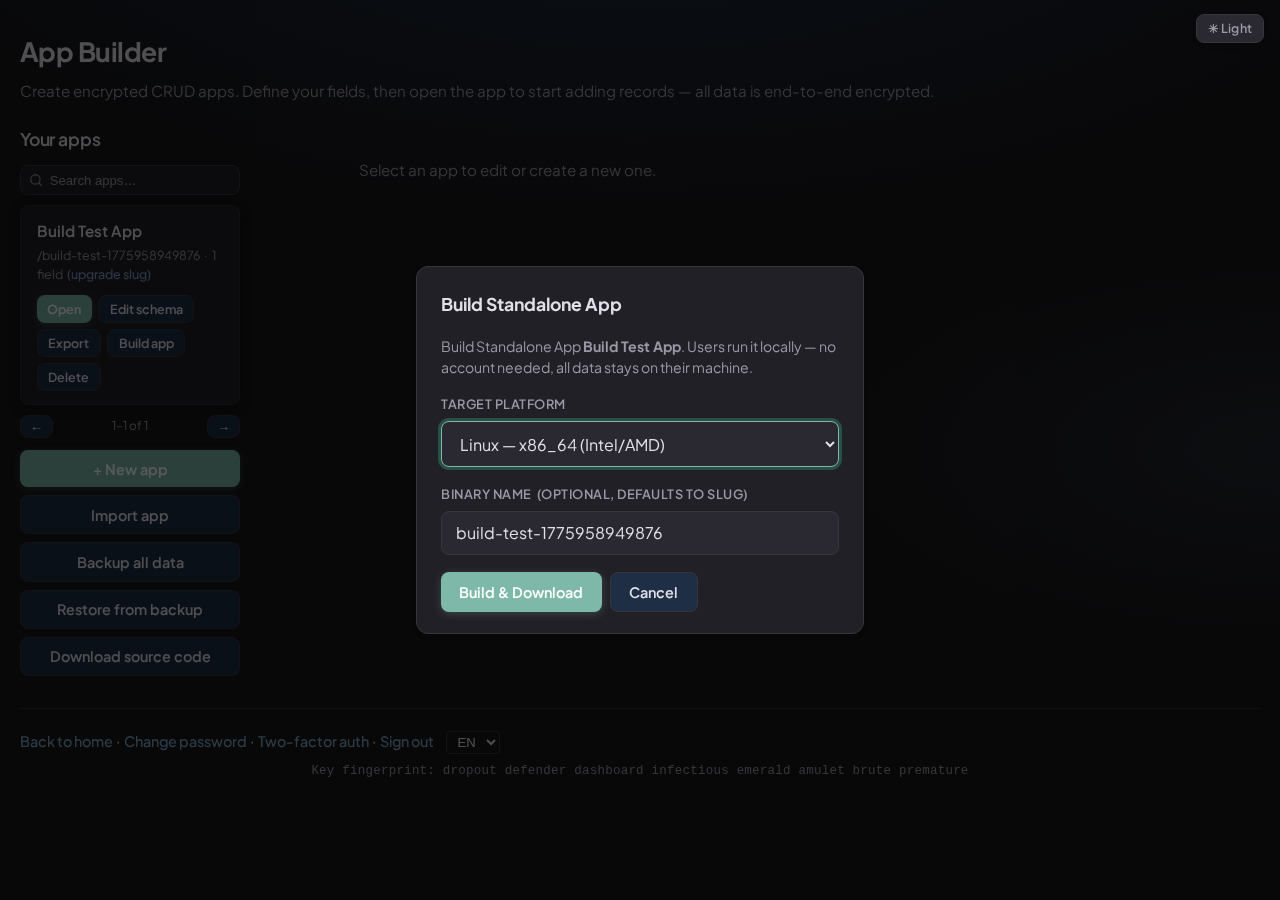
Two-factor authentication
Optional TOTP (time-based one-time password) support means even a stolen password
can't be used to log in alone. The 6-digit code changes every 30 seconds and is
generated by an app on your phone.
Backup codes let you regain access if you lose your authenticator. Password reset
works without breaking any of your encrypted data.
Authenticator app codes · Backup codes
🚦
Rate limiting on login
The login endpoint limits repeated failed attempts and temporarily blocks abusive
traffic. This helps slow down automated password-guessing attacks.
Temporary lockouts on repeated failures
🍪
Sessions via secure cookies
Authentication uses HttpOnly session cookies, which means JavaScript on
the page cannot read the session token. This protects against a common attack called
cross-site scripting (XSS).
CSRF tokens protect all state-changing requests (POST, PUT, DELETE) from being
triggered by malicious third-party websites.
HttpOnly cookies · CSRF tokens · SameSite policy
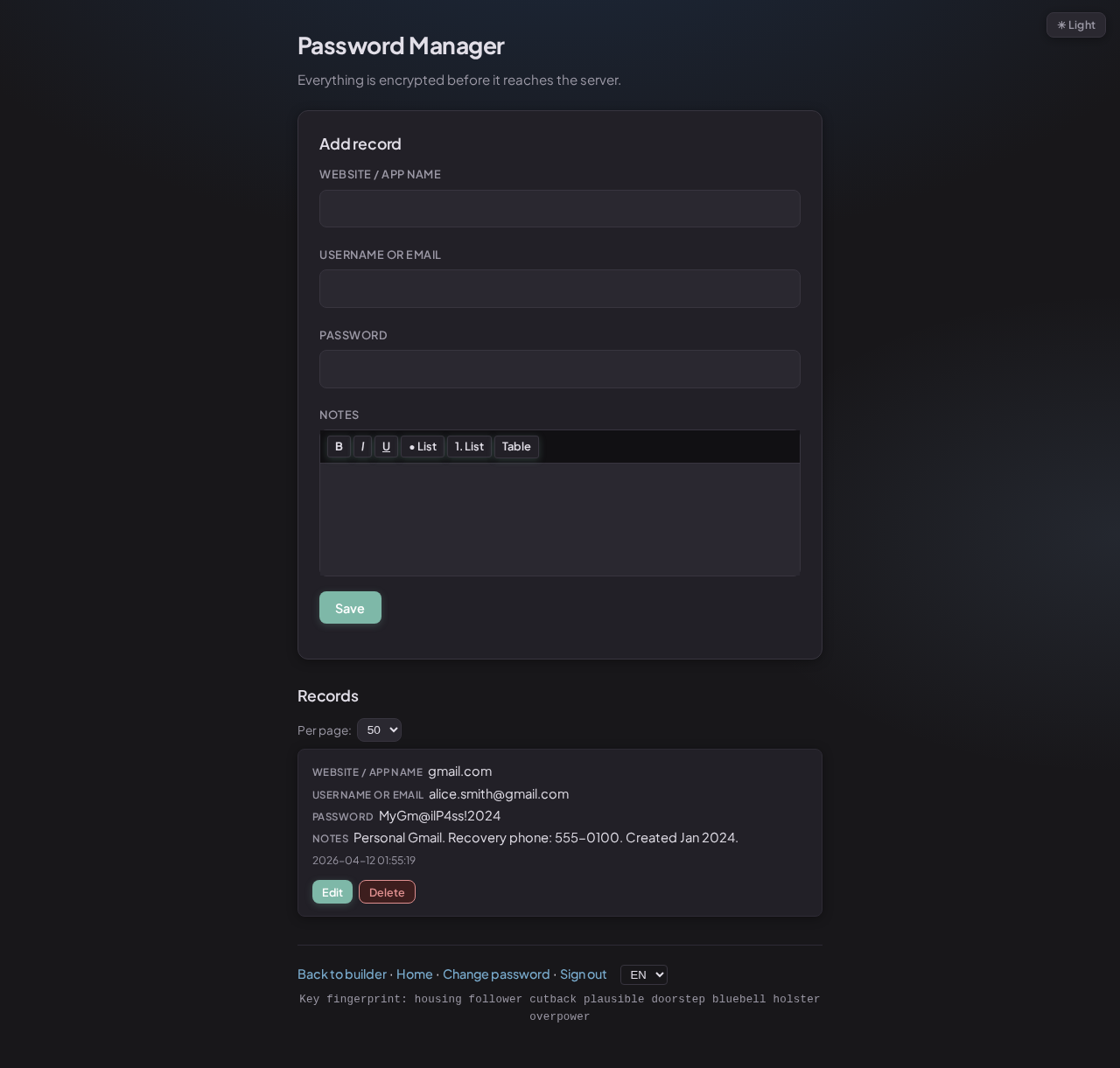
Here's every piece of data stored in the database and whether anyone with a copy of
that database could read your information.